linux如何禁止频繁访问的ip访问nginx
导读:本文共2648.5字符,通常情况下阅读需要9分钟。同时您也可以点击右侧朗读,来听本文内容。按键盘←(左) →(右) 方向键可以翻页。
摘要: 实验环境版本:redhat6.5ip:172.16.1.100,172.16.10软件:nginx172.16.1.10部署nginx[root@localhosttools]#lsnginx-1.11.2.tar.gz[root@localhost... ...
音频解说
目录
(为您整理了一些要点),点击可以直达。
实验环境
版本:redhat6.5
ip:172.16.1.100,172.16.10
软件:nginx
172.16.1.10部署nginx
[root@localhosttools]#lsnginx-1.11.2.tar.gz[root@localhosttools]#yuminstallgccgcc-c++makeautomakeautoconflibtoolpcre*zlibopensslopenssl-devel[root@localhosttools]#tarxfnginx-1.11.2.tar.gz[root@localhosttools]#lsnginx-1.11.2nginx-1.11.2.tar.gz[root@localhosttools]#cdnginx-1.11.2[root@localhostnginx-1.11.2]#lsautoCHANGESCHANGES.ruconfconfigurecontribhtmlLICENSEmanREADMEsrc[root@localhostnginx-1.11.2]#./configure[root@localhostnginx-1.11.2]#make[root@localhostnginx-1.11.2]#makeinstall
测试nginx服务
[root@localhost~]#curl-I172.16.1.100HTTP/1.1200OKServer:nginx/1.11.2Date:Mon,17Aug202009:36:29GMTContent-Type:text/htmlContent-Length:15Last-Modified:Mon,17Aug202009:36:19GMTConnection:keep-aliveETag:"5f3a4f93-f"Accept-Ranges:bytes
nginx 可以正常访问。
接下来,假设172.16.1.100是黑客主机,频繁访问nginx服务
模拟172.16.1.100访问10次172.16.1.10
172.16.1.100
[root@localhost~]#ab-c1-n10http://172.16.1.10/ThisisApacheBench,Version2.3Copyright1996AdamTwiss,ZeusTechnologyLtd,http://www.zeustech.net/LicensedtoTheApacheSoftwareFoundation,http://www.apache.org/Benchmarking172.16.1.10(bepatient).....doneServerSoftware:nginx/1.11.2ServerHostname:172.16.1.10ServerPort:80DocumentPath:/DocumentLength:612bytesConcurrencyLevel:1Timetakenfortests:0.016secondsCompleterequests:10Failedrequests:0Writeerrors:0Totaltransferred:8450bytesHTMLtransferred:6120bytesRequestspersecond:617.02[#/sec](mean)Timeperrequest:1.621[ms](mean)Timeperrequest:1.621[ms](mean,acrossallconcurrentrequests)Transferrate:509.16[Kbytes/sec]receivedConnectionTimes(ms)minmean[+/-sd]medianmaxConnect:010.301Processing:110.312Waiting:010.311Total:110.512ERROR:Themedianandmeanfortheinitialconnectiontimearemorethantwicethestandarddeviationapart.TheseresultsareNOTreliable.Percentageoftherequestsservedwithinacertaintime(ms)50%166%175%180%290%295%298%299%2100%2(longestrequest)
查看nginx日志
172.16.1.10
[root@localhost~]#tail/usr/local/nginx/logs/access.log172.16.1.100--[26/Jul/2020:05:58:24+0800]"GET/HTTP/1.0"200612"-""ApacheBench/2.3"172.16.1.100--[26/Jul/2020:05:58:24+0800]"GET/HTTP/1.0"200612"-""ApacheBench/2.3"172.16.1.100--[26/Jul/2020:05:58:24+0800]"GET/HTTP/1.0"200612"-""ApacheBench/2.3"172.16.1.100--[26/Jul/2020:05:58:24+0800]"GET/HTTP/1.0"200612"-""ApacheBench/2.3"172.16.1.100--[26/Jul/2020:05:58:24+0800]"GET/HTTP/1.0"200612"-""ApacheBench/2.3"172.16.1.100--[26/Jul/2020:05:58:24+0800]"GET/HTTP/1.0"200612"-""ApacheBench/2.3"172.16.1.100--[26/Jul/2020:05:58:24+0800]"GET/HTTP/1.0"200612"-""ApacheBench/2.3"172.16.1.100--[26/Jul/2020:05:58:24+0800]"GET/HTTP/1.0"200612"-""ApacheBench/2.3"172.16.1.100--[26/Jul/2020:05:58:24+0800]"GET/HTTP/1.0"200612"-""ApacheBench/2.3"172.16.1.100--[26/Jul/2020:05:58:24+0800]"GET/HTTP/1.0"200612"-""ApacheBench/2.3"
由此可见,一秒钟之内172.16.1.100访问了nginx10次,接下来禁止掉这个问题ip
通过iptables限制ip访问
172.16.1.10
[root@localhost~]#iptables-IINPUT-s172.16.1.100-ptcp--dport80-jDROP
172.16.1.100
[root@localhost~]#curl172.16.1.10curl:(7)Failedconnectto172.16.1.10:80;连接超时
此时172.16.1.100再也不能访问nginx
nginx配置文件限制
172.16.1.10
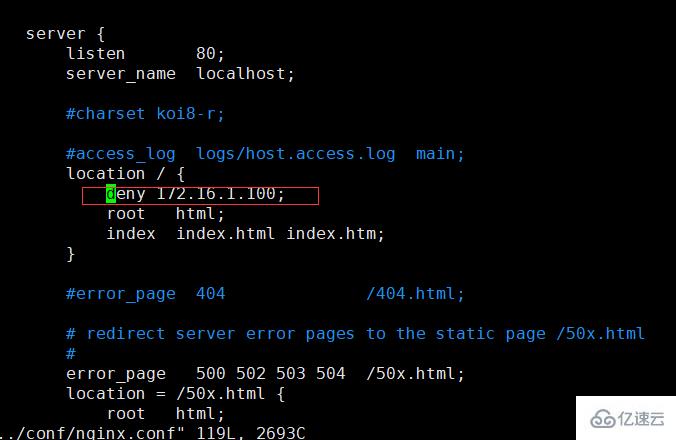
172.16.1.100
[root@localhost~]#curl-I172.16.1.10HTTP/1.1403ForbiddenServer:nginx/1.11.2Date:Sat,25Jul202023:12:06GMTContent-Type:text/htmlContent-Length:169Connection:keep-alive
</div> <div class="zixun-tj-product adv-bottom"></div> </div> </div> <div class="prve-next-news">本文:
linux如何禁止频繁访问的ip访问nginx的详细内容,希望对您有所帮助,信息来源于网络。